What is a VPN?
A VPN or virtual private network allows you to establish secure connection to another network over the Internet. VPNs can be used to access region-restricted websites, shield your browsing activity on public Wi-Fi. VPN’s are very popular these days, but not for the reasons originally created. They were essentially just a way to connect business networks together securely over the internet or allow you to access a business network from home
How does a VPN work?
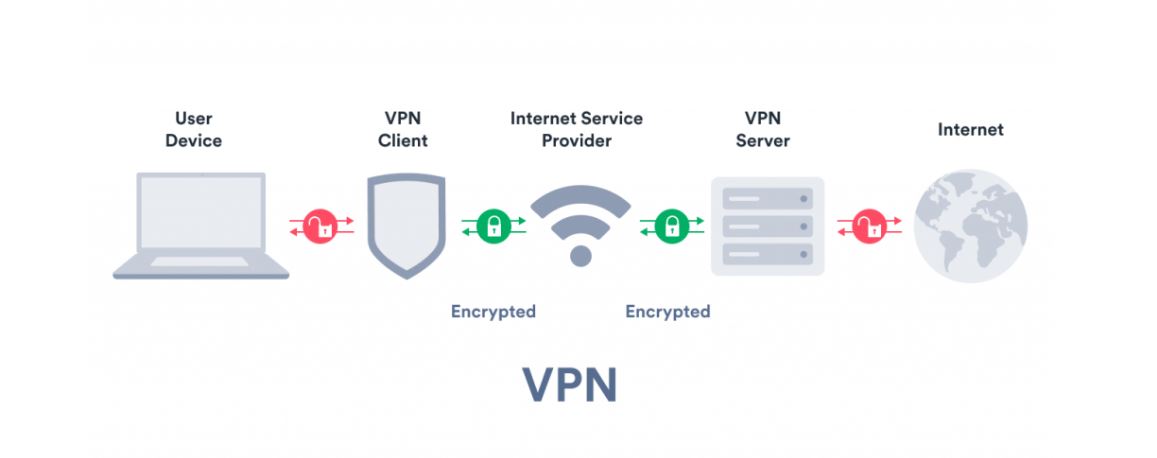
When you connect to the internet via VPN, it creates secure virtual tunnel between yourself and one of its servers. This tunnel is then used to transfer all your internet traffic that originates from your apps and websites. To ensure the tunneling process is secure, the VPN client and VPN server encrypt their data using a shared key. The client and server do this every time the data travels through the encrypted tunnel. That way, no one can see the content of the traffic. VPN ensures that your IP address, location, and online identity remain hidden from internet service providers and third-party websites
A VPN server is just a standard server configured with specific software. This ensures that only people with the correct customer software can connect to it. If you try to connect to VPN server it will ask for authentication that will make you the correct customer. Once verified, all traffic goes through this server. For anyone watching from the outside, they only see random internet data passing through the server. Hence, your whereabouts remain unknown
Examples of VPN use

Access Business Network While Traveling:
VPNs are often used by business travelers to access their business network including all local network resources while on the road. Local resources don’t have to be directly exposed to the Internet that increases security
Access Home Network While Traveling:
You can also set up your own VPN to access your network while traveling. It allows you to access windows desktop remotely over the internet, use local local shares and play games over the internet as if you were on the same network
Hide Your Browsing Activity From Your Local Network and ISP:
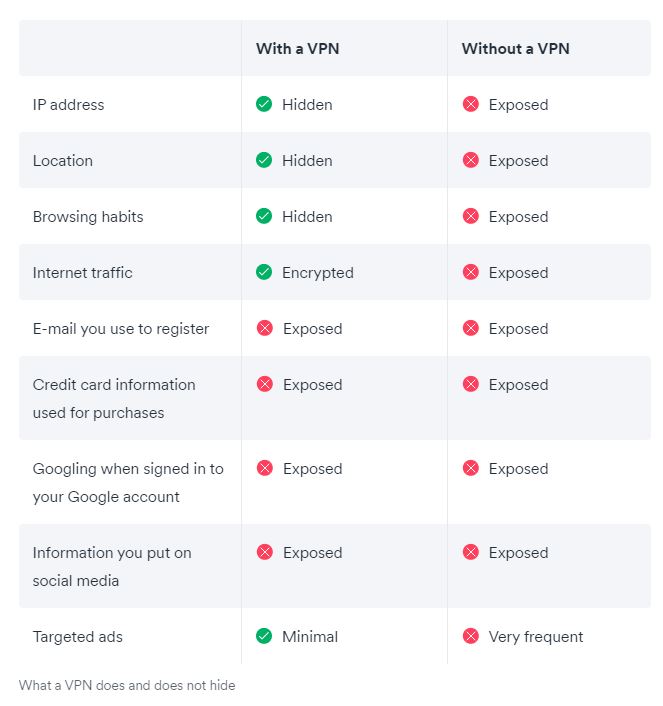
If you use a public Wi-Fi connection, your browsing activity is visible on non-HTTPS websites for everyone nearby. If you want to hide browsing activities for a little more privacy you can connect to a VPN. The local network will only see a secure VPN connection only. All other traffic travels over VPN connectivity. While this can be used to bypass the monitoring connection by your Internet service provider VPN providers may log traffic at their end
Access Geo-Blocked Websites:
VPNs allow you to look like you are connected to the internet from the country of your choice, simply choosing a VPN server from your chosen country tricks the website allowing you to access limited area services
Bypass Internet Censorship:
Many Chinese people use VPP’s to bypass China’s great firewall and access the entire Internet
Downloading Files:
Many people use VPN connections to download files via BitTorrent. This can actually be useful even if you are downloading a completely legal torrent – if your ISP is throttling BitTorrent and making it very slow you can use BitTorrent in VPN to get faster speeds. The same is true for other types of traffic your ISP may interfere with
What kind of VPNs are there?
There are many different types of VPN two common types are:
SSL VPN:
Often not all employees of a company have access to a company laptop that they can use to work from home. During the Coronavirus crisis in the spring of 2020, many companies faced difficulties not having enough equipment for their employees. In such cases it often resorts to using a private device (PC, laptop, tablet, mobile phone). In this case, companies will again SSL-VPN solution that is usually implemented through a corresponding hardware box. The prerequisite is usually an HTML-5-enabled browser used to call a company login page. HTML-5-enabled browsers are available for virtually any operating system. Access is protected by username and password
Site-to-site VPN:
VPN Site to Site is essentially a private network designed to hide private intranets and allow users of these secure networks to access each other’s resources. This is useful if you have multiple locations in your company, each with your local network (LAN) connected to WAN (Wide Area Network). Site-to-site VPN’s are also useful if you have two separate intranets between them you want to send files without users of one intranet explicitly accessing another. Site-to-site VP’s are mainly used in large companies. They are complicated to implement and do not offer the same flexibility as SSL VPNs. However, they are the most effective way to ensure communication in and between large sectors
VPN disadvantages
As with any type of technology, there are also some disadvantages to using VPN
Potentially slower speed:
Your web traffic goes through more steps than usual when connected via VPN, so there can be slowdown in perception. Since this has always been the #1 complaint developers have noticed. Many successes have had optimization of speed and performance, so that their users can stream and play fluidly without hiccups
QoS challenges: QoS stands for “quality of service” and describes the performance of a service or network. VPN does not yet have a standard for measuring and reporting such measurements in place. Without a metric to analyze, you need to rely on professional reviews and word of mouth to learn what’s most reliable
VPN blocks: Some businesses are wised to VPNs to fight back companies began to block access from known VPN IP addresses
No cookie protection: While VPN does your job of keeping you private and encrypted, it’s not possible for a VPN to block cookies, some of which are necessary to make sites work properly. The bad type of cookies, tracking cookies, can still be stored in your browser and identify who you are. Luckily you can easily delete tracking cookies. Or better, use a private browser that prevents you from tracking cookies from following you across the Internet
Not total privacy: While VPN blocks your ISP, governments, hackers, and other snoops from seeing your data your VPN provider can see their internet activities if they want to. That’s why choosing a reliable provider that doesn’t keep logs is so important
Alternatives
A Virtual Private Network isn’t the only tool that can increase your privacy, security, and/or freedom online
Tor
Tor (short for The Onion Router) is a free network of servers, or nodes, that randomly route internet traffic between each other to obscure the origin of the data. Using Tor can significantly increase your anonymity, and using Tor in conjunction with a VPN creates the best privacy protection possible. However the tor’s biggest drawback is speed. Because your traffic is relayed through a few hops, you’ll probably find it unpleasant to stream, download, or share files with Tor
Proxy services
Proxy server is any intermediary between your device and the Internet, however most “proxy services” you will find are quite slow and do not offer any privacy or security benefits.
So-called free proxy services are particularly risky as many other ways to monetize your data find such as selling it to third parties
Neither Tor or proxy service can replace the benefits of a VPN and is still the best privacy solution for most people.
For more tech news visit our tech page





