Fancy Bear – Part three of The Hacking Series


Who is Fancy Bear?
Techniques
Timeline of Fancy Bear attacks
Although security researchers believe the group have been active since at least 2004 Fancy Bear first appeared in a report by Trend Micro on October 22 2014
2014 Operation Pawn Storm
Operation Pawn Storm named after the chess strategy was a long running series of attacks using the sofacy malware
2014 Attacks on prominent journalists
From mid-2014 until the fall of 2017 Fancy Bear targeted numerous journalists in the United States, Ukraine, Russia, Moldova, the Baltics, and other countries who had written articles about Vladimir Putin and the Kremlin
2014 Attacks on German parliament
Fancy Bear conducted a cyber attack on the German parliament that began in December 2014 and completely paralyzed the Bundestag’s IT infrastructure To resolve the situation, the entire parliament had to be taken offline for days. IT experts estimate that a total of 16 gigabytes of data were downloaded from Parliament as part of the attack
2015 US Military wives death threats
Five wives of U.S. military personnel received death threats from a hacker group calling itself CyberCaliphate, claiming to be an Islamic State affiliate, This was later discovered to have been a false flag attack by Fancy Bear, when the victims’ email addresses were found to have been in the Fancy Bear phishing target list
2015 French television hack
On April 8, 2015, French television network TV5Monde was the victim of a cyber-attack by a hacker group calling itself CyberCaliphate and claiming to have ties to the terrorist organization Islamic State of Iraq and the Levant (ISIL). French investigators later discounted the theory that militant Islamists were behind the cyber-attack, instead suspecting the involvement of Fancy Bear
2015 root9B report
Security firm root9B released a report on Fancy Bear in May 2015 announcing its discovery of a targeted spear phishing attack aimed at financial institutions. The report listed international banking institutions that were targeted, including the United Bank for Africa, Bank of America, TD Bank, and UAE Bank. According to the root9B, preparations for the attacks started in June 2014 and the malware used “bore specific signatures that have historically been unique to only one organization, Sofacy”
2015 EFF spoof, White House and NATO attack
In August 2015, Fancy Bear used a zero-day exploit of Java, spoofing the Electronic Frontier Foundation and launching attacks on the White House and NATO. The hackers used a spear phishing attack, directing emails to the false URL
2016 German Government
The group is also suspected to be behind a spear phishing attack in August 2016 on members of the Bundestag and multiple political parties. Authorities feared that sensitive information could be gathered by hackers to later manipulate the public ahead of elections due in September 2017
2016 World Anti-Doping Agency
In August 2016 the World Anti-Doping Agency reported the receipt of phishing emails sent to users of its database claiming to be official WADA communications requesting their login details. After reviewing the two domains provided by WADA, it was found that the websites’ registration and hosting information were consistent with the Russian hacking group Fancy Bear
2016 Dutch Safety Board and Bellingcat
Bellingcat, a group researching the shooting down of Malaysia Airlines Flight 17 over Ukraine were targeted by numerous spear phishing emails. The messages were fake Gmail security notices with Bit.ly and TinyCC shortened URLs. According to ThreatConnect, some of the phishing emails had originated from servers that Fancy Bear had used in previous attacks elsewhere
The group targeted the Dutch Safety Board, the body conducting the official investigation into the crash, before and after the release of the board’s final report. They set up fake SFTP and VPN servers to mimic the board’s own servers, likely for the purpose of spearphishing usernames and passwords
2016 Democratic National Committee
Fancy Bear carried out spear phishing attacks on email addresses associated with the US political Democratic National Committee. Phishing emails that were mainly directed at old email addresses of 2008 Democratic campaign staffers began to arrive. One important account was breached and 50,000 emails stolen, The phishing attacks intensified in April, although the hackers seemed to become suddenly inactive for the day on April 15 which in Russia was a holiday in honor of the military’s electronic warfare services. The malware used in the attack sent stolen data to the same servers that were used for the group’s 2015 attack on the German parliament
2016 Windows zero-day
On October 31, 2016, Google’s Threat Analysis Group revealed a zero-day vulnerability in most Microsoft Windows versions . Microsoft acknowledged the vulnerability and explained that a “low-volume spear-phishing campaign” targeting specific users had utilized “two zero-day vulnerabilities in Adobe Flash and the down-level Windows kernel.” Microsoft pointed to Fancy Bear as the threat actor, referring to the group by their in-house code name STRONTIUM

February 2017 IAAF hack
The officials of International Association of Athletics Federations (IAAF) stated in April 2017 that its servers had been hacked by the “Fancy Bear” group. The attack was detected by cybersecurity firm Context Information Security which identified that an unauthorised remote access to IAAF’s servers had taken place. IAAF stated that the hackers had accessed the Therapeutic Use Exemption applications, needed to use medications prohibited by WADA
2016 – 2017 German and French elections
Researchers from Trend Micro in 2017 released a report outlining attempts by Fancy Bear to target groups related to the election campaigns of Emmanuel Macron and Angela Merkel. According to the report, they targeted the Macron campaign with phishing and attempting to install malware on their site. French government cybersecurity agency ANSSI confirmed these attacks took place, but could not confirm APT28’s responsibility. Marine Le Pen’s campaign does not appear to have been targeted by APT28, possibly indicating Russian preference for her campaign. Putin had previously touted the benefits to Russia if Marine Le Pen were elected.
2018 International Olympic Committee
On January 10, 2018, the “Fancy Bears Hack Team” online persona leaked what appeared to be stolen International Olympic Committee (IOC) and U.S. Olympic Committee emails related to the IOC’s banning of Russian athletes from the 2018 Winter Olympics as a sanction for Russia’s systematic doping program
2018 United States conservative groups
The software company Microsoft reported in August 2018 that the group had attempted to steal data from political organizations such as the International Republican Institute and the Hudson Institute think tanks. The attacks were thwarted when Microsoft security staff won control of six net domains. In its announcement Microsoft advised that “we currently have no evidence these domains were used in any successful attacks before the DCU transferred control of them, nor do we have evidence to indicate the identity of the ultimate targets of any planned attack involving these domains”
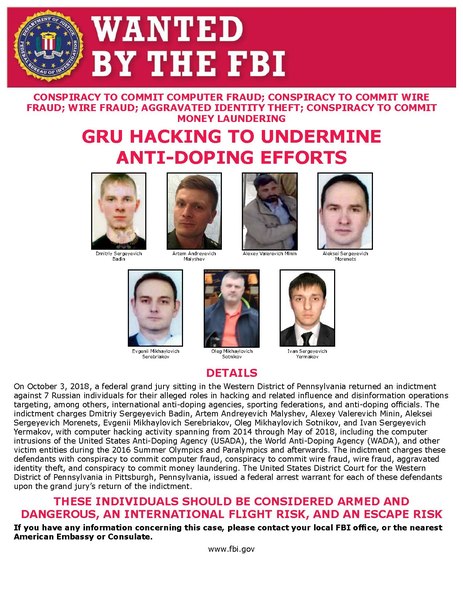
2018 US Indictments
In October 2018, an indictment by a U.S. federal grand jury of seven Russian men, all GRU officers were unsealed. The indictment states that from December 2014 until a least May 2018, the GRU officers conspired to conduct “persistent and sophisticated computer intrusions affecting U.S. persons, corporate entities, international organizations, and their respective employees located around the world, based on their strategic interest to the Russian government. The U.S. Department of Justice stated that the conspiracy, among other goals, aimed “to publicize stolen information as part of an influence and disinformation campaign designed to undermine, retaliate against, and otherwise delegitimize” the efforts of the World Anti-Doping Agency to expose extensive doping of Russian athletes sponsored by the Russian government
2020 Strategic Czech institution
In 2020 Czech National Cyber and Information Security Agency reported cyber espionage incident in an unnamed strategic institution, possibly the Ministry of Foreign Affairs, carried out most likely by Fancy Bear
2020 Arrest warrant of German authorities
In 2020 German officials named Dimitri Badin, an officer of the GRU and suspected member of APT28 as the main suspect for the cyber-attacks on the Bundestag from 2015
2020 Norwegian Parliament attack
In August 2020 the Norwegian Parliament discovered a “significant cyber attack” on their e-mail system, Norway’s foreign minister, Ine Marie Eriksen Søreide accused Russia for the attack.
Conclusion
