We have received information showing that Pendar Kooshk Imen Company has been hacked by an unknown group, resulting in a breach of the company’s supposedly secure communications with the national banking sector. This intrusion means that this seemingly new group calling themselves Setaregan Azadi, now has access to the highly confidential information of millions of Iranians, jeopardizing their financial security. Undoubtedly, this incident will be a source of shame for the company, which claims on its website to aim to “enhance the level of information security in the country’s technology sector”.
Is it worth noting that this is the third major incident in the Iranian banking sector in the past two months, less than a year since banks and exchange offices were also targeted by cyber attacks.
According to the published information, the companies and entities affected by this security breach include:
- Banks (Melli, Sepah, Tejarat, Middle East)
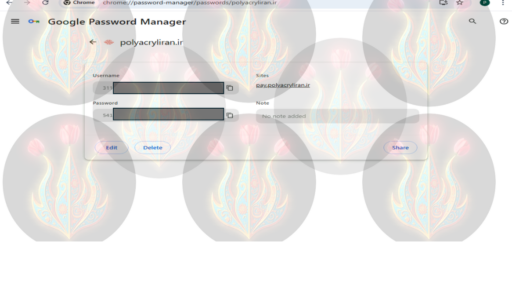
- Polyacryl Iran, including its websites polyacryliran.ir, polyacryl.ir and polyacryiran.com
- fipcoiran.com, manufacturer of synthetic fiber raw materials
- Various government entities and private concerns
Currently the affiliation and motivation of this group is unknown, but images posted on GitHub show a blue emblem in the shape of roses on fire, which may indicate a new anti-regime group. Analyzing the technical specifications of the attack, the group appears to be relatively sophisticated.
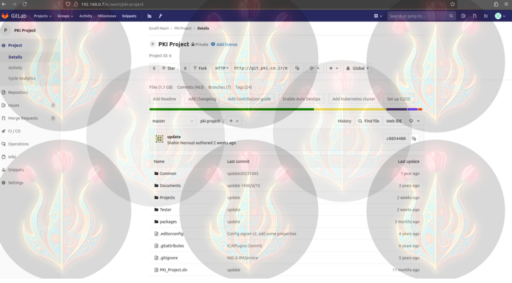
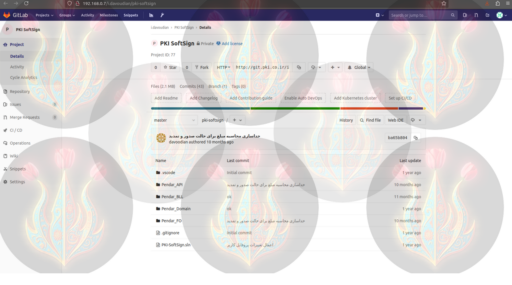
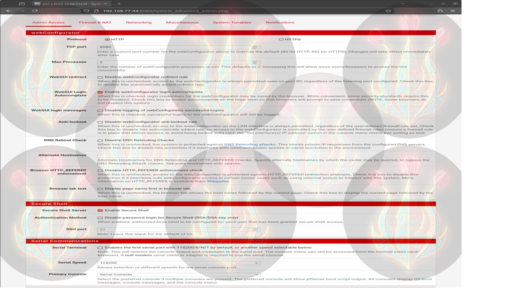
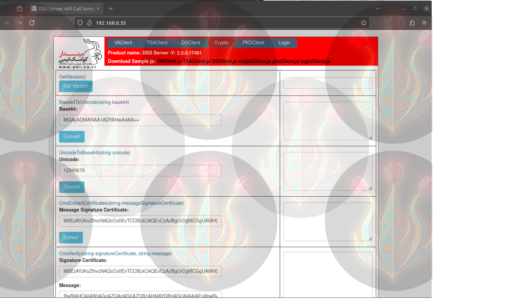
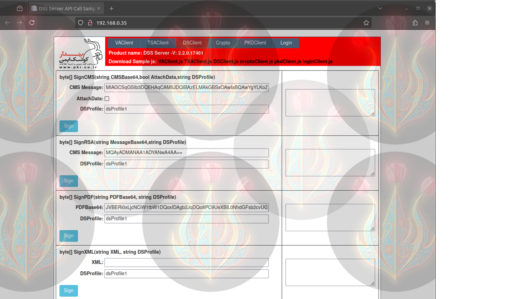
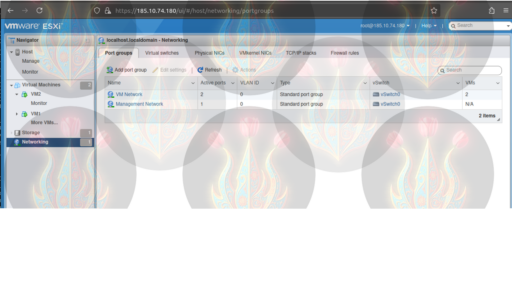
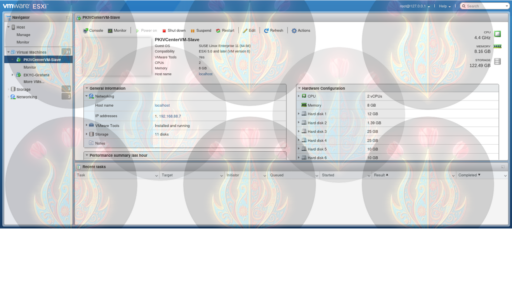
The images below, initially posted on GitHub, show that the group has access to the following systems:
- PKI’s ESXi platform, used to manage the company’s infrastructure
- Compromised customer information
- APIs for encryption services used in PKI operations
- Internal company source code
- Exposed admin accounts such as [email protected]
- Full control of customer web hosting
These images seem to prove that the group has penetrated the network of PKI, therefore posing a serious threat to any organization or company that uses its services. Furthermore, the group may have access to commercial systems and vital infrastructure, such as the company’s authentication system, which could provide opportunity to launch spearfishing attacks.
Before publishing this report, we contacted PKI for a response. A company representative told us the following:
“Please be informed that the matter has been reported to the competent authorities in accordance with legal requirements, and full cooperation is underway. A formal report will be published once the origin and perpetrators of the attack are identified and the technical investigations are completed and approved by the relevant organizations”.
If you have more information about the Setaregan Azadi hacking group, please share it with us confidentially.
To view all the released information, visit the group’s GitHub page: https://github.com/SetarehganAzadi/1