MuddyWater

List of names used by the industry:
- Seedworm
- Mango Sandstorm
- Static Kitten
- MERCURY
- Earth Vetala
- TEMP.Zagros
- TA450
- Boggy Serpens
Date founded:
MuddyWater was first publicly identified in 2017 and is known to use a wide range of tools and techniques in its operations. The name “MuddyWater” was coined by Palo Alto Networks in 2017 because the group’s early campaigns were difficult to attribute and were often confused with other intrusion sets.
Affiliation:
MuddyWater is an Iranian state backed group that is affiliated with MOIS.
Social media handles/websites:
N/A
Previous operations:
2017 – First reported by Palo Alto Networks a series of malicious files were discovered affecting systems in nine countries including Saudi Arabia, Iraq, Israel, India, Georgia and the USA. These files were almost identical to malware that had previously been found in Saudi Arabia Government computers and had been adjusted according to the target region, often using logos or branches of local government, prompting users to bypass security controls and enable macros.
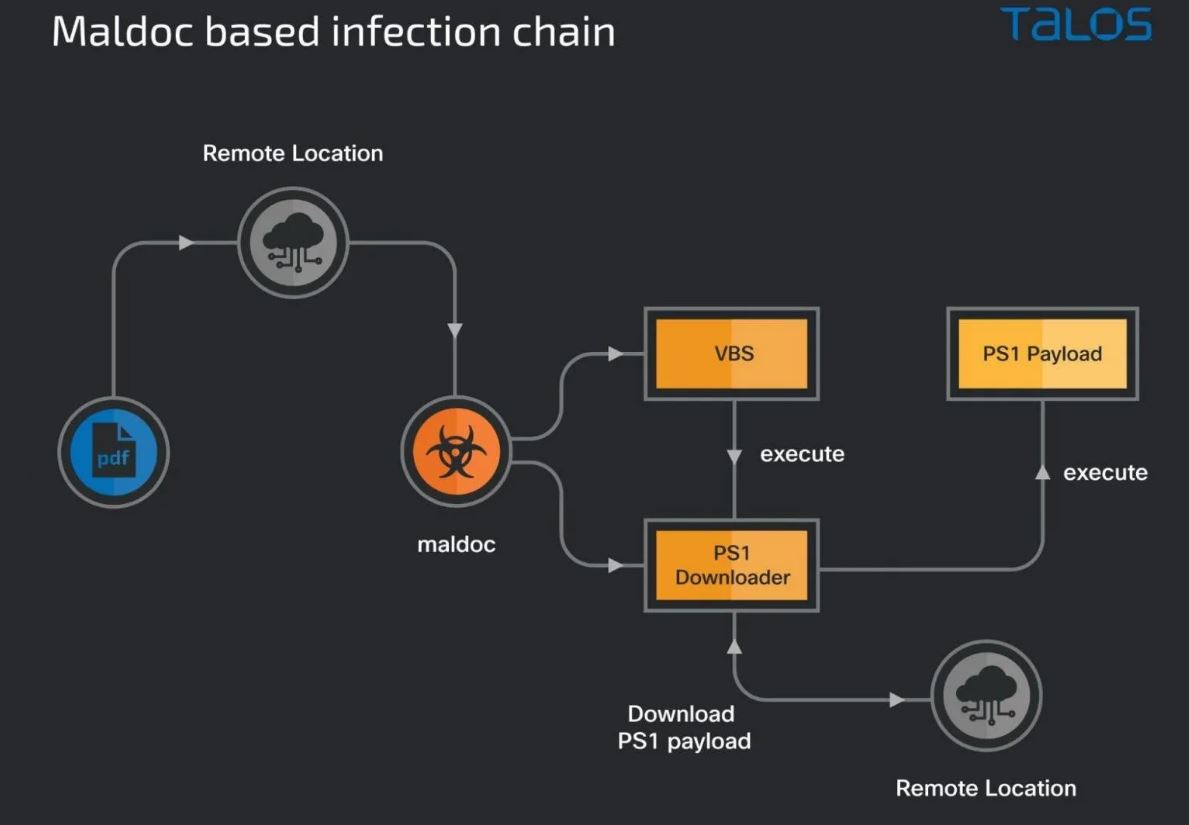
2018 – MuddyWater targeted organizations in Turkey, Pakistan and Tajikistan with a similar campaign that had targeted Saudi Arabia. The attackers used documents that mimicked government organizations such as the ministry of internal affairs or the republic of Tajikistan, even using official government emblems. Researchers at cyber security company Trend Micro found text and file names in the Tajik language attempting to target individuals working for government and telecommunication companies. Each document use social engineering to trick potential victims into clicking to enable macros and activate hidden payloads. While some of the payloads were observed embedded inside documents others were also downloaded from the internet after the lure was clicked.
2018 – The group was caught targeting victims in Lebanon and Oman leveraging compromised domains to deliver macro-enabled documents that were designed to look like resume applications from the ministry of justice in Lebanon or Saudi Arabia. Like the other attacks once enabled these macros activated payloads that further infected the victims systems.
2019 – A large number of spear-phishing documents were discovered that appeared to target government, military, education and telecommunication institutions in Jordan, Turkey, Azerbaijan and Pakistan. Like before these documents relied on social engineering to persuade users to enable macros. The group relied on a range of compromised hosts to deliver their attacks however cyber security experts at tech company Securelist were able to to observe a number of OPSEC mistakes made by the attacker, these mistakes would continue to plague the group until the present day.
2019 – The group targeted Kurdish groups and various organizations in Turkey affiliated with the army and defense sector. The initial infection vector was via emails attached with malicious word documents. Below is a screen capture of a document sent to the Kurdish party. The blurred image is an example of a fake official document of the Kurdistan Regional Government. The target is prompted to enable editing or enable content to properly view the documents content, however this executes an embedded malicious macro command.
2020 – MuddyWater was detected attempting to hack dozens of government agencies and telecommunications companies in Iraq, Kuwait, Turkey and the United Arab Emirates, The attacks appear to be trying to smuggle key data from the organizations they managed to breach. These attacks were the first time the group started to use a new tool called PowGoop which once installed on a victims computer allowed the installation of other programs capable of siphoning data off of networks. During this time the group began to shift away from solely scripting-based tooling such as Powershell and moved from .NET and custom C++ payloads.
2021 – MuddyWater was officially linked to the Ministry of Intelligence and Security by US Cyber Command after an operation by the group was discovered targeting Turkish telecommunication and government IT systems. Much like all the previous attacks the group used malicious PDFs and Microsoft office documents as the initial infection vector, the bait documents masqueraded as legitimate documents from the Turkish Health and Interior Ministries, Upon opening the documents a malicious PowerShell based down loader gave the group an initial foothold into the targets network. Once inside the network a second PowerShell script in the metadata of the weaponized document downloads a third malicious script that ultimately runs on the infected endpoint. This attack was the first time the group was observed using canary tokens in the macro code to track successful infections, evade sandbox-based detection systems and detected if the payload servers were being blocked.
2023 – Group teamed up with DEV-1084 to conduct destructive attacks under the pretext of deploying ransomware.
2024 – MuddyWater increased its activity against Israeli targets after the start of the Israel-Hamas war. In campaigns observed in March and April 2024, the group used compromised email accounts and PDF files containing embedded links to deliver malicious archives and remote monitoring tools to Israeli employees at multinational firms.
June 2024 – Iran International published a report disclosing the indentities of several key members from MuddyWater: Mohammad Reza Khroosh, Younes Valiaei and Mohammad Khosh’lahan.

20 August 2025 – Deploys multi stage phishing campaign to target CFO’s and finance executives. Masqueraded as a Rothschild & Co recruiter, the group employed Firebase-hosted phishing pages with custom CAPTCHA challenges, malicious VBS scripts and multi stage payload delivery to silently deploy remote management capabilities.
October 2025 – Used Qilin ransomware to target an Israeli government hospital.
October 2025 – MuddyWater carried out a sophisticated spearphishing attack that used a compromised mailbox to distribute a custom backdoor known as Phoenix to international organizations in the Middle East and North Africa, targeting over 100 government entities.
November 2025 – Linked to attacks that targeted academics with expertise on the Middle East and other foreign policy experts.
February 2026 – Attributed to an attack inside the network of a major South Korean electronics manufacturer, as part of a sprawling early-year espionage campaign affecting at least nine organizations across four continents.
Other targets included government agencies and an international airport in the Middle East, Southeast Asian industrial manufacturers, a Latin American financial-services provider, and educational institutions in multiple countries.
February 2026 – MuddyWater launched a campaign dubbed Operation Olalampo, deploying new malware variants and leveraging Telegram bots for command-and-control. The campaign targeted multiple organizations and individuals primarily in the Middle East and North Africa and used new malware families including CHAR, GhostFetch, HTTP_VIP and GhostBackDoor, with one variant communicating through a Telegram bot used for command and control.
6 March 2026 – MuddyWater hacked into the networks of several US organizations, including an aerospace and defense contractor. As part of the campaign the group deployed a new backdoor dubbed Dindoor on the network of the software supplier’s Israeli branch, the US bank and a Canadian NGO.
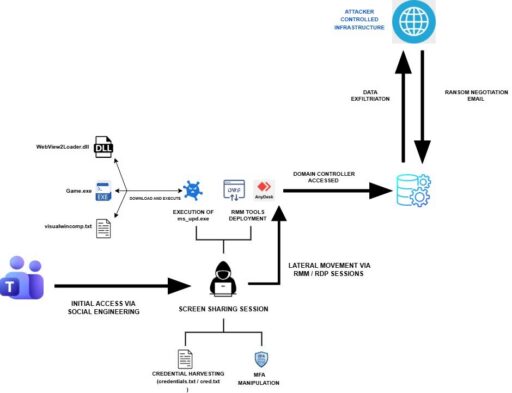
6 May 2026 – The group was attributed to an intrusion masquerading as a Chaos ransomware attack. The threat group engaged with the victim organization via Microsoft Teams, establishing screen-sharing sessions for access to users’ assets. They stole credentials, manipulated the MFA protections and compromised accounts. The threat actors then ent emails to users for extortion claiming to have stolen information and demanding a ransom.
26 May 2026 – The group were linked to a campaign targeting nine organizations in nine countries. The attackers relied on DLL side-loading using legitimately signed Fortemedia and SentinelOne binaries to execute malicious DLLs while masquerading as benign software.
Tactics/Techniques/Tradecraft/Procedures (TTP’s):
- Targeting high value intelligence entities in the Middle East as part of espionage operations
- Spearphishing and credential theft
- Deploying ransomware and exploitation of vulnerabilities
Sources:
- attack.mitre.org/groups/G0069/
- securityweek.com/iranian-apt-intrusion-masquerades-as-chaos-ransomware-attack
- securityweek.com/iranian-apt-intrusion-masquerades-as-chaos-ransomware-attack
- securityweek.com/iranian-apt-hacks-us-airport-bank-software-company
- thehackernews.com/2026/05/muddywater-uses-microsoft-teams-to.html
- hunt.io/blog/apt-muddywater-deploys-multi-stage-phishing-to-target-cfos
- security.com/threat-intelligence/iran-cyber-threats-activity-us
- group.9b.com/blog/muddywater-operations-olalampo/
- www.security.com/threat-intelligence/iran-seedworm-electronics
- Wikipedia.org/wiki/MuddyWater_(hackergroup)
- thehackernews.com/2026/05/muddywater-uses-dll-side-loading-in.html

