Charming Kitten
Charming Kitten is an Iranian state-aligned cyber actor that seeks to target human rights activists, academic researchers, media outlets and individuals who are of interest to Iran’s government and security agencies. Unlike other Iranian APT groups focussed on disruptive cyber attacks, Charming Kitten focusses on cyber espionage, credential theft, surveillance and influence operations. Charming Kitten focusses on operations in the Middle East and North Africa but strategically extends its influence to Europe, the Americas and the Asia-Pacific.
List of names used by the industry:
- APT35
- Ajax Security (FireEye)
- NewsBeef (KasperSky)
- Magic Hound
- Educated Manticore
- Ballistic Bobcat
- CharmingCypress
- TunnelVision
- Mint Sandstorm (Microsoft)
- Phosphorus
- بچه گربه ملوس یا چارمینگ کیتن
Date founded:
- Around the end of 2013
Affiliation:
Charming Kitten has been affiliated with APT34, APT33 and Rocket Kitten. Charming Kitten operates under the influence of the Islamic Revolutionary Guard Corps and Iran’s intelligence agencies, engaged in cyber-enabled espionage campaigns that align with Iran’s geo-political interests.
Social media handles/websites:
N/A
Previous operations:
- 2014 – 2016 – Operation Newcaster – The group created fake journalist personas and social media accounts to interact with and spy on Western military personnel and policymakers. They made a fake news website and reposted articles from BBC, Reuters, Associated Press and populated profiles with fictitious personal content on Youtube, Facebook, Twitter, LinkedIn, Google and Blogger to build rapport. Used spear-phishing emails and attacks of infecting individuals’ devices with malware for data exfiltration. Over 3 years the group is believed to have over 2000 victims.
- 2015-Present – Espionage on nuclear negotiations, the group targeted nuclear policy experts, diplomats and think tanks involved in Iran nuclear deal discussions.
- 2018-Present – Cyber attacks on dissidents and journalists, the group has infiltrated opposition groups and human rights activists, leading to surveillance, arrests, and censorship of dissenting voices. These attacks have impacted political discourse, intelligence operations, and diplomatic relations between Iran and Western nations.
- 2019-2021 – The group launched credential theft campaigns against the US and European officials, sending phishing attacks impersonating security officials to collect login credentials from the US and European government staff.
- 2023-2024 – Between 2023 and 2024 Charming Kitten intensified its operations, adopting more sophisticated social-engineering tactics and multi-stage infection chains.
Tactics/Techniques/Tradecraft/Procedures (TTP’s):
- Espionage tactics include spear-phishing emails impersonating journalists, policymakers and academic intuitions, fake websites and social media profiles mimicking legitimate platforms
- Credential theft via malicious login pages for Google, Microsoft and social media accounts
Key People of Interest:
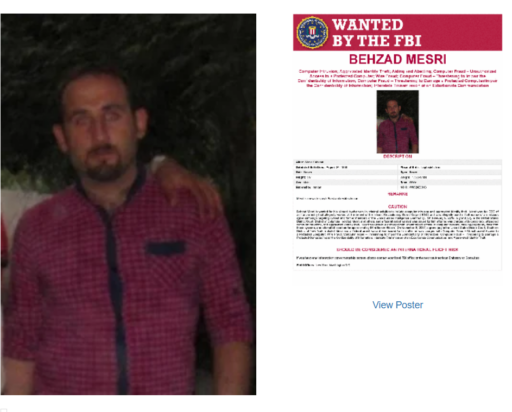
- Behzad Mesri (alias Mr Smith/Skote Vahshat) – Mesri is a long-standing actor linked to Iranian offensive cyber operations, reportedly involved in the 2017 HBO breach and several state-sponsored attacks. U.S. Department of Justice filings describe him as part of a broader ecosystem supporting IRGC-linked operations.
- Mohammadamin Keshvari (aliases: “ArYaIeIrAn” / ArYaIeIrAn email handles shown in reporting -Open-source reporting and vendor analysis have connected a persona using the handle ArYaIeIrAn to domain-management activity and to an individual identified as Mohammadamin Keshvari. That reporting links the persona to Mahanserver (an Iran-based web-hosting provider) and suggests a role managing malicious domains and infrastructure used in phishing and staging. These identifications are based on OSINT techniques (profile-picture correlation, domain registration/redirect patterns, and hosting relationships) and should be treated as vendor-level assessments.
- Mohammad Rasoul Akbari (alias: “ra3ou1”) — Mahanserver – Publicly available profiles and reporting identify Mohammad Rasoul Akbari as the founder/CEO of Mahanserver, an Iranian hosting provider that has been observed in vendor reporting as hosting domains and services used in Charming Kitten-attributed operations. Analysts have noted social-graph connections (mutual follows/friends) between Akbari and other alleged operators in open-source material; vendor reporting also references Mahanserver infrastructure as being operationally useful to the group. Public business profiles for Akbari corroborate his role with Mahanserver.
Major Breach of Charming Kitten — Internal Leak Exposure
In what appears to be one of the most significant exposures of an Iranian state-sponsored cyber operation to date, an anonymous whistleblower or rival actor has publicly released a cache of internal documents, employee data, and operational records belonging to Charming Kitten. The leak was published on GitHub by a group with the alias “KittenBusters”.
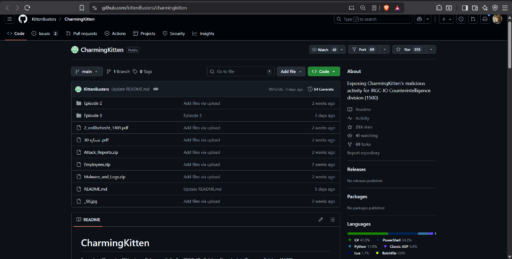
Sources:
cybersecuritynews.com/charming-kitten-leaks-key-personnel
blog.narimangharib.com/posts/2025%2F09%2F09%2F1759266283728lang=en
ginc.org/apt35/
darkatlas.io/blog/inside-apt35-irans-state-sponsored-cyber-espionage

