Iranian TYRANT Ransomware
A new type of ransomware have been discovered on October 16 2017 which appears to be Iranian. The Tyrant Ransomware is a data encryption Trojan that is classified as a mid-tier crypto-threat. The threat appears to be used in attacks on home users and small businesses that lack proper cyber protections.
Analysis of compromised systems clearly shows that the Tyrant Ransomware targeted Farsi-speaking users based in South-East and South Asia -outside of Iran, Farsi is also spoken in countries such as Iraq, Pakistan, India and the United Arab Emirates-. This may appear to be from Iran but also could be an attempt to blame Iran. However, some of the payment options -see below- are clearly Iranian. It is not known who the actual source is and it is possible that the developers behind the Tyrant Ransomware may be deliberately limiting the first attack wave.

The Tyrant Ransomware appears to spread via spam emails that may invite users to download and open a PDF, DOCX, and ZIP file with interesting informations such as a purchase confirmation notice, an invoice or a job application. Tyrant Ransomware is based on the Ramsomeer Ransomware -or DUMB– code, which targeted Turkish speakers.
It is possible that the same programmers make both Trojans. The new variant runs as ‘DUMB.exe’ and uses custom cryptographic algorithms to lock data. The Tyrant Ransomware is very different from the majority of Trojans based on HiddenTear such as the KimcilWare Ransomware and the CyberSplitter 2.0 Ransomware.
Tyrant does the following:
- Scans the compromised machine for data
- Makes a list of the objects suitable for encryption, generates a pair of encryption and decryption keys, and then encrypts those files
- User access to the encrypted data is obstructed and so trying to access images, presentations, music, videos and any other content is impossible
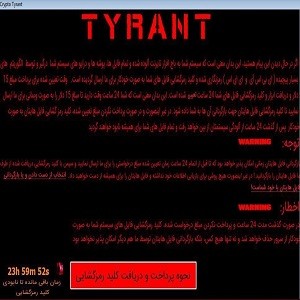
The ransomware message in a program window is titled ‘Crypto Tyrant’ and has the message:
‘Your files are encrypted. You have 24 hours to pay the ransom of $15 dollars. The amount may increase further if 24 hours have elapsed… The file decryptor will be sent to you after receiving the payment. If you have any questions, please contact us by email, we will answer you…
Praise be to Allah in the heaven’

The ‘Crypto Tyrant’ window includes a 24 hours, which encourages users to quickly pay the $15 in Bitcoin for a decryptor. The team behind the Tyrant Ransomware claims to delete the decryption key if payment is not transferred to their BitCoin wallet address. The small amount of money may be intended to look like amounts a friend may want for a favour. The only reliable way to restore your data is to install any previous backups and then use good Anti-malware softwares to remove all traces of the Tyrant from your system.
The payments option include obvious Iranian domains: exchanging.ir and webmoney724.ir and the contact details are a Telegram username of @Ttyperns and email address of [email protected]
Anti-virus softwares support rules to detect Tyrant and may be detected as:
- MSIL.Trojan-Ransom.Pufmanhu.B
- MSIL/Crypdum.A!tr
- Ransom:Win32/Genasom
- Suspicious_GEN.F47V1015
- Trojan ( 005105431 )
- Trojan.Generic.DBEA218
- a variant of MSIL/Filecoder.DY
- malicious_confidence_100% (W)
- malware (ai score=67)
Reference: https://www.certcc.ir/news/entry/12223
