IRLeaks

List of names used by the industry:
IRLeaks (no other names identified)
Date founded:
Telegram channel was created 13 June 2023
Affiliation:
Researchers have analyzed data from irleaks attacks and determined that irleaks’ activity aligns with actions of more organized, advanced threat actors rather than opportunistic, individual hackers. No conclusive evidence that the group is linked to a nation-state and officials have stated that IRLeaks is affiliated with neither the US nor Israel.
Social media handles/websites:
- Telegram – @IRLeaks (old account) current Telegram account is @irleaks_admin
Previous operations:
The group announced their existence is July 2023 declaring that their main activity was to penetrate important Iranian sites and sell information. The group did not claim any ideological motivation for their activities.
- July 2023 – Breach of multiple insurance firms: Asia Insurance (25,799,452 records for $10,000), Razi Insurance (11,015,722 records for $4,000), Sina Insurance (6,013,416 records for $1,500), and Hafez Insurance (431,947 records). The data allegedly included: name, surname, date of birth, father’s name, phone/mobile number, ID number, national code and more.
- 11 July 2023 – The group hacked and defaced the website of the Imam Relief Committee’s Economic Community (ecemdad.ir) and shared a link to the archive.org capture of their work.
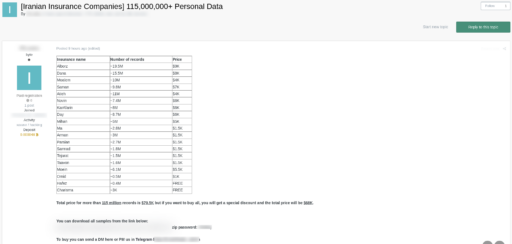
- August 2023 – The group advertised an updated list of insurance records for sale. The list included over 115 million records of information from the following companies: Alborz Insurance, Dana Insurance, Moallem Insurance, Saman Insurance, Atiye Insurance, Novin Insurance, Karfarin Insurance, Dey Insurance, Mihan Insurance, Ma Insurance, Arman Insurance, Parsian Insurance, Sarmed Insurance, Tejarat Insurance, Tawan Insurance, Moeen Insurance, Omid Insurance, Hafez Insurance and Karizma Insurance. The prices of the data ranged from $1,000-$10,000 depending on the number of records corresponding to each company.
- 2 September 2023 – The group announced that the company Tapsi had been hacked and that they were selling information including the passenger data (name, surname, mobile number, city, email address) driver data (name, surname, national code, city, mobile number), trip data (over 136 million trips including passenger ID, full address of origin and destination, short address of origin and destination, geographical characteristics of origin and destination), and source code of Tapsi company products. Tapsi’s CEO tweeted confirming that hackers had stolen the information from their systems. A follow up post on IRLeaks’ telegram channel implied that the group had tried to negotiate with Tapsi for two weeks prior to the public announcement of the sale.
- 30 December 2023 – The group announced that they had hacked SnappFood. They claimed to have extensive data from the company, including user information (20 million records), order information (260 million orders), courier information (35,000 records), payment information (600,000 records), courier trips information (160 million records), vendor information (240,000 records), and product order information (880 million records). On 31 December 2023, SnappFood acknowledged the breach publicly and disclosed that Iran’s Cyber Police (FATA) was actively working to identify the breach’s source. On 1 January 2024, the group announced that after successful negotiations with the SnappFood team that the dataset would not be sold.

- 1 June 2024 – The group announced they had hacked the Hajj and Pilgrimage organization. They claimed to have information about pilgrims from pilgrimages that took place during the years 1363 to 1403 (roughly 1984 to 2024). This information included biographical details such as name, surname, father’s name, date of birth, place of birth, ID, card number, national code, marital status, occupation and contact information. The dataset allegedly also included other collateral details such as flight, insurance and payment information. Other datasets for sale also included government and officials’ dispatches, quota dispatches, NAJA forces’ dispatches, Basij forces’ dispatches, clerics’ dispatches and the source code of the organization’s applications and services. The total data volume was 1.25 terabytes. On 3 June 2024, the group announced that following failed negotiations the dataset was available to purchase on exploit.in and onniforums.com.
- 9 July 2024 – The group announced they had hacked Otaghak. They claimed to have reservation information, billing information, messages and chats, user information, payment information, detailed information about bookable places, user search information, banking information, and more. The group shared a sample of the dataset on the site mega.nz. On 10 July 2024, the group announced that following successful negotiations with the Otaghak team the data had not and would not be sold for anyone.
- August 2024 – The group allegedly targeted the Iranian banking system. The attack forced banks to shut down cash machines across the company. The group stole data which consisted on the personal account and credit card data of millions of Iranians. The group initially demanded $10 million but apparently later settled for a smaller sum. The group allegedly entered the banks’ servers via a company called Tosan (which provides digital services to Iran’s financial sector). As many as 20 private banks and financial institutions were hit including the Iranian central bank, Bank of Industry and Mines, Mehr Interest-Free Bank, Sarmayeh Bank, and more. Allegedly Tosan was ultimately forced to pay the IRLeaks ransom (at least $3 million). Interestingly, IRLeaks never claimed responsibility for the attack on their Telegram channel but this attack has been widely attributed to the group.
- 3 October 2024 – The group shared an announced to their Telegram channel that due to Telegram’s new policies of working directly with governments and that they could not idenitfy a suitable alternative they had decided to permanently stop the group’s activities. They highlighted that any further activity under the name #IRLeaks is not related to them and that the previously available data (Insurance, Tapsi and Hajj) would no longer be available to purchase.
- 18 February 2026 – The group announced that they were relaunching as a warning to incompetent administrators. They claimed that their previous channel (@irleaks) was no longer accessible but that they would continue on their new channel (@irleaks_admin). The group announced that the dataset of Tapsi, the Insurance companies, and the Hajj organization was once again available to be purchased. On 19 February 2026, the group shared the prices for the data: Insurance companies: $60k, Tapsi: $40, Hajj organization: $80k.
Tactics/Techniques/Tradecraft/Procedures (TTP’s):
- Extortion tactics
- Targeting on major corporations (e.g. Insurance companies, financial institutions).
- Ransomware attacks and extortion
- Social engineering
- Supply chain attacks
- Selling data on the darkweb
Reseachers allegedly identified a potentially compromised employee of SnappFood, whose computer was infected with the “StealC” infostealer. This is an information stealer that is advertised and sold as a Malware-as-a-service on Russian-speaking underground forums. For more information on this malware please see https://malpedia.caad.fkie.fraunhofer.de/details/win.stealc. Analysis also indicates that a targeted approach such as social engineering/spear-phishing may have aided initial access.
Sources:
- Telegram channel
- Hackread.com/iranian-food-delivery-snappfood-cyber-attack
- Themoloch.com/analysis/irleaks-threat-actor-claims-massive-dataleaks-against-major-iranian-companies-draws-speculation
- Infostealers.com/article/mysterious-hacker-strikes-iran-with-major-cyberattacks-against-industry-leading-companies
- Politico.eu/article/iran-millions-ransom-massive-cyberattack-banks
- Wikipedia.org/wiki/IRLeaks_attacks_on_iranian_banks
